Prevent Wire Transfer Fraud in Real Estate - Use StealthMail!
Real estate wire fraud is one of the fastest-rising crimes in the United States.
The FBI, your local police department, the bank are all powerless to stop this fraud from happening and can only warn people about the wire fraud post factum.
Awareness is useful, but the real estate industry needs a solution to stop email compromise and exploitation to save their clients and reputation.

Microsoft recommends StealthMail to its customers
Wire Fraud Keeps Growing
- 11,677 registered real estate/rental fraud victims in 2019 combined monetary loss of $221 million.
- 114,702 reported cases fell victim to phishing campaigns in 2019.
- 11,300 reported victims and a $150 million loss in 2018.
Wire Fraud Red Flags
- Inconsistencies in email addresses and domain names.
- Sense of urgency in a message.
- Last-minute changes to the wiring instructions and bank account details.
Solution
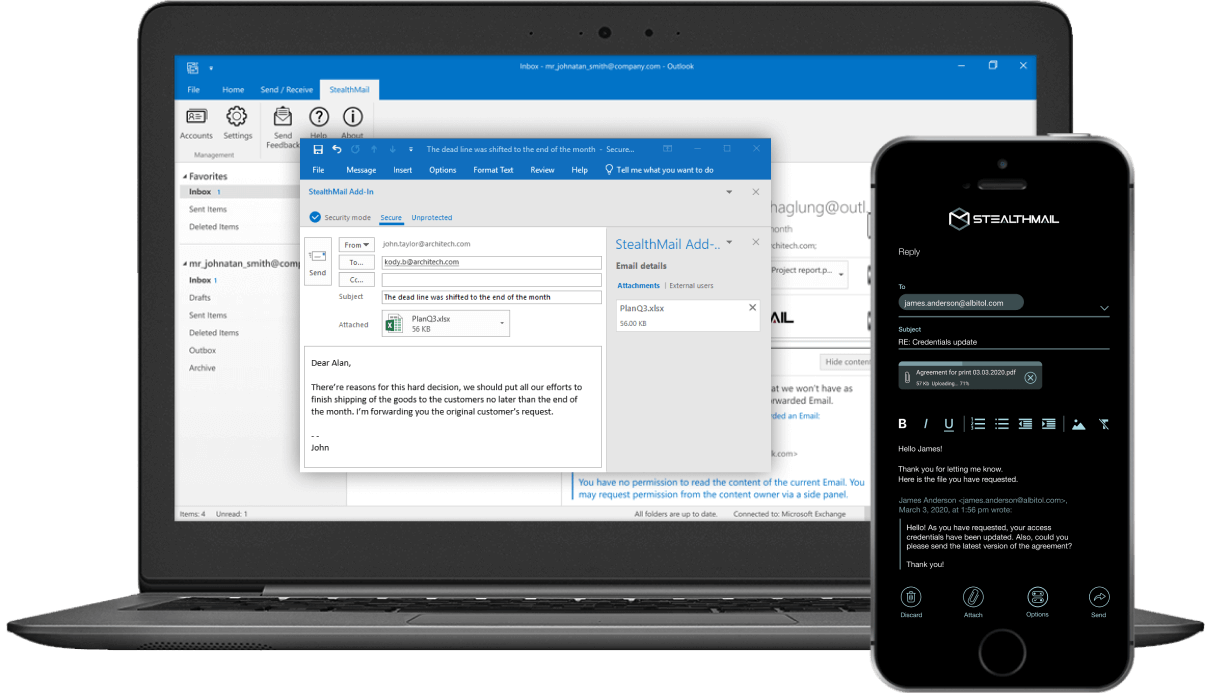
The StealthMail email security solution allows companies to mitigate risks associated with wire fraud by encrypting sensitive email content and attachments, controlling encryption keys, managing access rights to confidential data.
Technical Specifications
Encryption keys
ECC 512+
bit elliptic curve
Data transfer
TWOFISH 256
bit
Messaging
512
bit HMAC key
Signature and Auth
RSA 8192
bit
Data storage
AES 256
bit
Passwords hash
SHA-3 512
bit
How It Works
Your confidential data remains secured in your encrypted storage in Azure Cloud, and is never exposed to the threats of the Public Internet.
- Individually encrypts your email content and attachments and generates a unique identifier that refers to the message.
- Transmits it through dedicated secure communication channels.
- Allows authorized users to get access to encrypted content and attachments.

Why StealthMail?
- Identifies senders and recipients by using the digital signature of the message.
- Secures sensitive data with advanced encryption algorithms.
- Protects data even in case of compromised email infrastructure, device, or account credentials.
- Enforces stringent email authentication methods.
- Prohibits forwarding, copying, screen recording, and replying options to both internal and external addresses.
- Keeps data inside the company’s secure perimeter.
- Applies the second factor to establish a secure connection and enhance security.
Deployment
- StealthMail is deployed to Company’s Azure Cloud.
- Existing infrastructure is not affected.
- Deployment takes less than 2 hours.
Infrastructure Requirements
- Microsoft Azure Subscription.
- LDAP v2. (Microsoft Exchange, Office 365).
- Email clients: Microsoft Outlook 2013 | 2016, Outlook Office365.
Use StealthMail to Secure your Email Communications!
- 30 days of free use.
- Deployment takes place within an hour in the cloud of Microsoft Azure and does not affect the infrastructure of the company.
- License cost $ 15 per month per user.
Industries
Customers choose StealthMail to protect their confidential data against BEC/EAC attacks, data leaks, and to recall access rights of sent emails
Investments
Secure financial documents exchange
Energy
Protection of the accounting workflow
Automotive
Secure transactions
Retail
Protection of data related to orders and prices
Public Sector
Protection of data of national importance
Logistics
Secure correspondence between parties
Manufacturing
Secure correspondence and financial information
Banking
Secure correspondence with foreign branches
Media
Management and control of access rights
Minerals Industry
Secure legal documents
