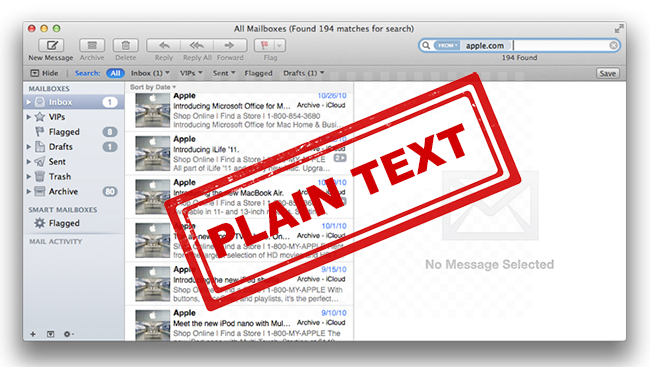
TL; DR: Apple Mail stores encrypted emails in plain text database, no private key required to read emails.
While investigating how macOS and Siri suggest information and contacts to its users, Bob Gendler, a former Apple Platform Engineer, discovered that snippets.db file from the Suggestions folder stored encrypted emails in plain text, even with Siri disabled.
That is a case of informational exposure, and this issue concerns corporations, governments, and regular users who encrypt their emails expecting protection. Additionally, Entities.db also stores records of names, emails, phone numbers, and data like signature blocks and stored forward information that allows quick access to your most sensitive data.
There Are At Least Three Ways To Disable Siri From Learning Apple Mail:
- Looking into Settings. System Preferences, Siri, Siri Suggestions & Privacy, Untick boxes for Apple Mail.
- Running a Terminal command “defaults write com.apple.suggestions SiriCanLearnFromAppBlacklist -array com.apple.mail”
- Deploying a System-Level configuration profile to turn off Siri. It is the only option to disable macOS and Siri from collecting Mail.
(!) Important note: disabling Siri and macOS from collecting Apple Mail doesn’t remove previously saved emails, just stops newer ones from collection.
This Behavior Is Incorrect, As Messages Should Always Be Encrypted.
Details matter when someone is trying to supply users with a secure platform that enables private communication. Guidelines presented below should serve as a reminder of encryption and data storing practices:
- Data in transit and at rest should always be encrypted.
- Encryption should be carried out on the client’s side.
- Only a client should have access to encryption keys and have full control over the storage with encrypted information.
To keep all your data safe and maintain email integrity, you may be interested to find out more about StealthMail solution, which is based on the criteria mentioned above. Discover more information about the inner workings of this solution, please go to StealthMail.com and download StealthMail DataSheet for free today.
Link copied to clipboard!